Microsoft Sentinel
AI-powered SIEM for modern SOCs.
Threats are outpacing traditional security tools
Cyber threats in Australia are growing in scale, speed, and sophistication. Yet most organisations are still operating with siloed tools, alert fatigue, and security teams stretched beyond capacity.
The answer is not more tools. It's a unified, intelligent platform that brings your entire digital estate into view and responds at machine speed.
Are these challenges familiar?

Alert fatigue is overwhelming your team.
Too many tools generate too many alerts, burying critical threats in the noise.

Siloed security tools leave blind spots.
On-premises, cloud, endpoints, and SaaS tools don't share signals. Attackers exploit the gaps.

SOC staffing and skills are scarce.
Recruiting and retaining experienced security analysts is expensive and increasingly difficult.

Legacy SIEM costs are spiraling.
Splunk and QRadar licensing, infrastructure, and maintenance costs are unsustainable at scale.
Microsoft Sentinel: The Cloud-Native SIEM Built for the AI Era.
Microsoft Sentinel is a cloud-native Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) platform. It ingests signals from across your entire digital estate — multi-cloud, on-premises, endpoints, and SaaS — and uses AI to detect, investigate, and respond to threats at scale.
Since 2025, Sentinel has been unified with Microsoft Defender XDR in a single Defender portal, giving security teams a consolidated console for SIEM and XDR capabilities. Microsoft was recognized as a Leader in the 2025 Gartner Magic Quadrant for SIEM.
SIEM + SOAR in One Platform
Collect, detect, investigate, and respond to threats — all within a single unified platform, without the cost of managing separate SOAR infrastructure.
AI-Driven Threat Detection
Built-in machine learning and Security Copilot integration surface threats faster than rule-based approaches, with explainable verdicts your team can act on.
Cloud-Scale Economics
Pay only for what you ingest, with commitment tiers offering up to 32% savings, and the new 50 GB tier making enterprise SIEM accessible for smaller organizations.
Microsoft Sentinel Core Capabilities
What can Microsoft Sentinel do for your organization? These core capabilities make Sentinel crucial for defending against emerging threats.
Comprehensive Threat Detection
Collect and analyse signals from 350+ data sources: firewalls, endpoints, cloud environments, identity platforms, and SaaS apps. Sentinel's codeless connector platform lets you onboard any source, with detection rules, dashboards, playbooks, and hunting queries available out of the box.
Security Copilot and Agentic AI
Microsoft Security Copilot brings generative AI to incident response, summarising incidents in natural language, suggesting remediation steps, and powering agentic workflows. The Sentinel MCP server connects AI agents to your security data for advanced automation.
Sentinel Graph
Sentinel graph builds a connected intelligence layer that links users, devices, alerts, behaviours, and incidents. It illuminates hidden attack paths and entity relationships, surfacing risks that traditional alert-based detection misses entirely.
Sentinel Data Lake
A cloud-scale security data foundation for cost-effective, long-term retention of high-volume telemetry. Supports direct ingestion from Microsoft Defender for Endpoint, Office, and Cloud Apps, without the cost of the full analytics tier, enabling richer historical investigation.
User and Entity Behaviour Analytics (UEBA)
The generally available UEBA behaviours layer aggregates security telemetry into clear, human-readable behavioural summaries. It detects insider threats and compromised accounts by identifying deviations from normal patterns across Microsoft and third-party sources, including AWS, GCP, and Okta.
SOAR and Automated Incident Response
200+ customisable playbooks automate routine response tasks, from account isolation to ticket creation, so your analysts focus on complex investigations. Machine learning correlates alerts into prioritised incidents, reducing mean time to respond across your environment.
Microsoft Sentinel in Action
Explore common use cases for Microsoft Sentinel that boost security operations and maintain compliance.
Threat Detection and Incident Response
Gain comprehensive visibility by collecting and correlating data from firewalls, endpoints, cloud environments, and identity platforms. Sentinel helps your team identify and prioritize threats and respond swiftly through automated playbooks.
Multi-Cloud Security Monitoring
Purpose-built for cloud environments, Sentinel provides native monitoring of Microsoft Azure alongside AWS, GCP, and hybrid infrastructure. New connectors include AWS Network Firewall, GCP Cloud Run, VPC Flow, and Palo Alto Prisma.
Centralized Log Management and Compliance
Consolidate all security logs — whether on-premises or cloud — into a single hub. Sentinel simplifies compliance, auditing, and long-term retention through its data lake, supporting major regulatory frameworks.
Insider Threat Detection
The UEBA behaviors layer analyzes cross-platform behavior patterns across Microsoft Entra ID, AWS, GCP, and Okta, surfacing anomalous access, data exfiltration, and privilege misuse before they escalate.
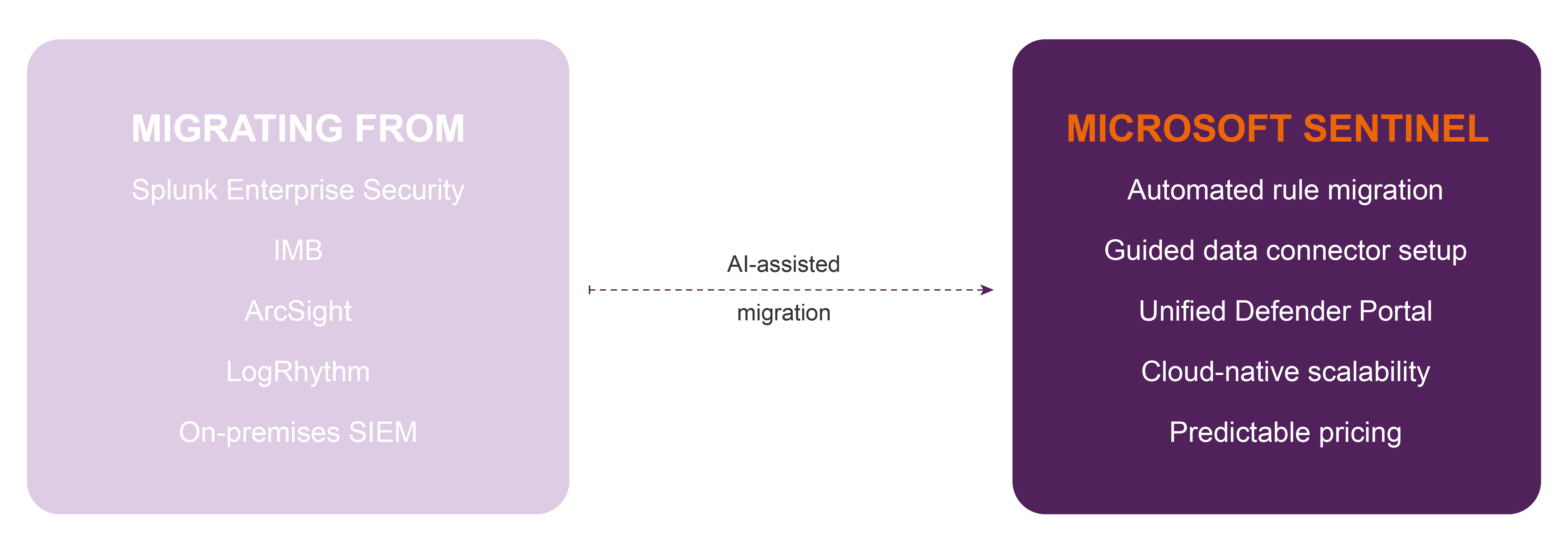
SIEM Migration from Splunk or QRadar
Modernize your SOC by migrating from legacy SIEM platforms. Microsoft's AI-assisted SIEM migration experience automates the translation of detection rules and the setup of data connectors. Professional Advantage provides full migration services and post-deployment support.
Proactive Threat Hunting
Give your analysts cutting-edge tools to actively investigate potential threats. Sentinel's KQL-based hunting queries, combined with Sentinel Graph and custom graph visualizations via the VS Code extension, enable deep investigation without writing detection rules from scratch.
Ready to leave Splunk or QRadar behind?
Microsoft's AI-assisted SIEM migration experience, combined with Professional Advantage's migration expertise,
makes moving to Sentinel faster and lower-risk than ever before.
Microsoft also offers free migration support through the Cloud Accelerate Factory program.
Contact us to find out if your organisation qualifies.
Want to find out more about Microsoft Sentinel?
1Staff boosts efficiency, increases productivity, generates insights, maximizes margins, and improves cash flow. Whether you are looking for a full suite of functionality, or a robust front office or back office to integrate with your existing solution, 1Staff has you covered.
Top Microsoft Sentinel FAQs
How long does a Microsoft Sentinel deployment take?
A standard Microsoft Sentinel deployment typically takes 4 to 12 weeks, depending on the size of your environment, the number of data sources, and the complexity of your detection and automation requirements.
Professional Advantage follows a structured methodology covering assessment, design, deployment, and handover, with ongoing managed services available post-deployment.
Can I integrate Microsoft Sentinel with my existing systems?
Yes. Sentinel can ingest data from Microsoft and third-party sources for unified SIEM and SOAR capabilities.
Popular third-party integrations with Microsoft Sentinel include, but are not limited to:
Security Solutions and Firewalls
|
Identity and Access Management
|
Email Security
|
Cloud Platform and SaaS
|
Endpoint Detection and Response (EDR)/XDR
|
Threat Intelligence
|
How does Microsoft Sentinel differ from traditional SIEM?
Here’s a side-by-side comparison of the differences between Microsoft Sentinel and traditional SIEM solutions.
| Feature | Microsoft Sentinel | Traditional SIEM |
|---|---|---|
| Deployment | Cloud-native (built on Azure). | On-premises or hybrid. |
| Scalability | Auto-scales with data volume and users. | Requires manual hardware or license upgrades. |
| Setup & Maintenance | Minimal setup; no infrastructure to manage. | High setup and ongoing maintenance costs. |
| Integration | Seamless with Microsoft 365, Azure, Defender, and third-party tools. | Often requires manual connectors and integrations. |
| Cost Model | Pay-as-you-go based on data ingestion. | Typically fixed or tiered licensing with high upfront cost. |
| Artificial Intelligence | Built-in AI/ML for automated threat detection and correlation. | Often limited or requires separate modules. |
| Automation | Native SOAR via Logic Apps and playbooks. | Requires third-party tools or custom scripting. |
| Updates & Upgrades | Continuous updates via Azure platform. | Periodic manual upgrades needed. |
| Multi-Cloud Support | Supports Azure, AWS, GCP, and hybrid environments. | Typically fixed or tiered licensing with high upfront cost. |
| Time to Value | Fast to deploy and derive insights. | Slower setup; longer time to operationalize. |
In simple terms:
- Sentinel is cloud-first, smarter, and faster to deploy—ideal for modern, hybrid, or cloud-native environments.
- Traditional SIEMs are infrastructure-heavy and often slower to adapt to evolving threats.
What is Microsoft Sentinel?
Microsoft Sentinel is a cloud-native Security Information and Event Management (SIEM) and Security Orchestration Automated Response (SOAR) solution built on Microsoft Azure. It helps organizations detect, investigate, and respond to security threats across their digital environment.
What makes Sentinel a powerful solution?
- Native integration with Microsoft 365 and Defender XDR tools.
- Real-time visibility into your environment’s security posture.
- Supports hybrid and multi-cloud environments (including AWS and Google Cloud).
- Pay-as-you-go pricing: —no infrastructure setup or upfront cost.
Key Features
| Feature | What it does |
|---|---|
| Data Collection | Connects to Microsoft 365, Azure, AWS, on-premises servers, firewalls, and more. |
| AI-powered Threat Detection | Uses machine learning and Microsoft threat intelligence to identify real threats. |
| Investigation Tools | Visualise attack chains, timelines, and correlations across data sources with Auxiliary Logs and Analytics Logs. |
| Automated Threat Response | Trigger playbooks (via Logic Apps) to respond to incidents automatically. |
| Scalability | As a cloud-native tool, it scales automatically with your data and workloads. |
Learn more about Microsoft Sentinel.